Key takeaways
- A long-range RFID skimmer is a device that a fraudster uses to intercept a connection between an RFID chip and a reader.
- Devices like keys, fobs, credit cards, and even passports use RFID technology.
- To protect yourself against RFID skimming, you can line your RFID devices with foil or invest in an RFID-blocking jacket or wallet.
- If you’re interested in providing your residents with an alternative to RFID credentials, you can invest in other methods of access control, like smartphone-based access.
Disclaimer: ButterflyMX access control fobs and key cards are encrypted and cannot be copied with RFID long-range skimmers. Furthermore, ButterflyMX does not endorse the use of RFID long-range skimmers.
Wireless technology has helped simplify tasks and make the world a more convenient place. Whether we’re talking about wireless headphones, contactless payments, or fobs and access control readers, wireless devices are becoming more prominent.
But is wireless technology like RFID safe? Turns out, you might have to watch out for intercepting tools, like RFID skimmers, that put your information at risk.
In this post, we explain what a long-range RFID skimmer is and how it works. Then, we help you protect yourself from RFID skimming by picking out alternative credential types.
This post covers:
- What is a long-range RFID skimmer?
- How do RFID skimmers work?
- How can you protect yourself against RFID skimming?
- Alternatives to RFID credentials
What is a long-range RFID skimmer?
A long-range RFID skimmer is a device that allows somebody to intercept a transmission between an RFID chip and its reader.
Across fields and industries, wireless technology is becoming more popular — and specific methods of wireless transmission come with benefits and drawbacks. You might have used Bluetooth, WiFi, or NFC (near-field communication) technology in your daily life. In fact, RFID, or Radio Frequency IDentification, is just another way to transmit information wirelessly.
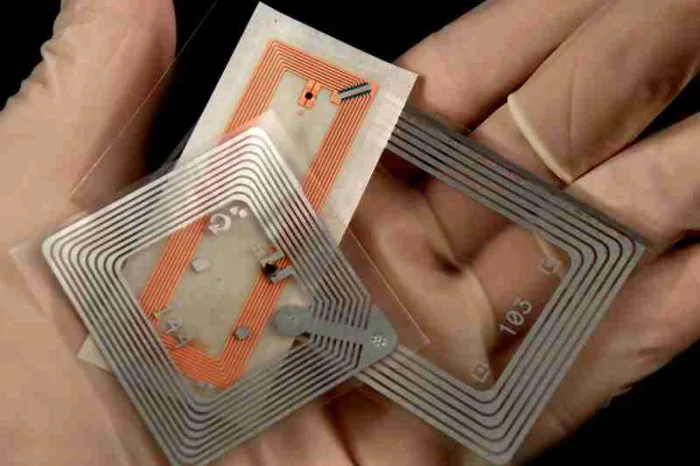
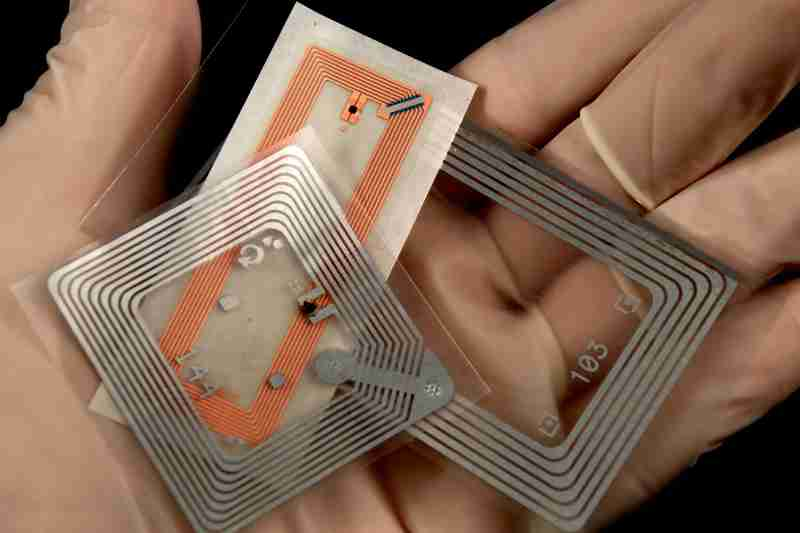
Devices that use RFID chips include:
- Credit cards
- Key cards
- Fobs
- Passports
Unfortunately, RFID manufacturers are up against scammers and fraudsters who want unsecured access to people’s transmissions.
In terms of RFID devices, criminals most often try to intercept credit card payment information or credential data that allows them access into a building.
Learn about the real estate cycle with ButterflyMX:
How do RFID skimmers work?
RFID skimmers work by triggering an RFID chip and recording the information stored on it.
There are two main types of RFID chips: active and passive. Active chips are connected to their own batteries, but passive chips need to be triggered by electromagnetic waves. As a result, a long-range passive RFID reader needs to be powerful enough to trigger a chip.
A fraudster might deploy a skimming device in a variety of ways. For example, a common method of RFID skimming is placing a reader close to where a lot of cards are frequently used, like near a commercial or residential property entrance. Then, as people present their cards, the skimmer records their card data. Then, the perpetrator clones the card using an app or programming device.
What is the longest range for an RFID reader?
Active RFID readers don’t rely on proximity. As a result, they can read from up to 300 feet away. However, if a signal repeater is employed, RFID readers can read up to 1,500 feet away.
What is the range of RFID skimmer?
Unfortunately, long-range RFID skimmers don’t need to be directly next to an RFID credential to read its information. Instead, most skimmers can read from a distance of up to 19 inches, or 50 centimeters. However, users can boost the power of an RFID skimmer with antennas or other long-range transmission technologies to try to collect data from further away.
How can you protect yourself against RFID skimming?
You can protect yourself against RFID skimming by covering your credential in foil or investing in RFID-blocking materials — such as carbon fiber.
However, while the technology to skim an RFID device certainly exists, the threat of a long-range RFID credit card skimmer is vastly overstated.
Even the best RFID long-range readers would struggle to successfully copy data illegitimately. Real-world conditions like distance, weather, and the presence of hundreds of other radio signals in an area make capturing somebody’s RFID data from afar much harder than it sounds.
While the technology to capture RFID data exists, criminals are more likely to use tactics like social engineering and phishing attempts to illegally obtain information.
With that being said, let’s further explore the best methods to protect yourself from a long-range RFID scanner:
Covering credentials in foil
While foil does succeed in blocking all RFID frequency ranges, this method comes with a few downsides. For instance, residents who want to use their credentials would have to spend time uncovering their credentials and covering them back up again.
Moreover, because one of the benefits of RFID access is the convenience of a single tap or touch, some residents may find that the security benefits of foil are too much of an inconvenience.
RFID-blocking materials
Manufacturers of RFID-resistant materials are producing a variety of products to meet consumer demands for safety and security. Security-conscious tenants can choose between RFID-blocking wallets, fanny packs, and even jeans.
Investing in encrypted access control
The best solution to prevent long-range RFID skimmers from impacting your property is to invest in an access control solution with encrypted credentials.
For example, ButterflyMX’s access control solution uses encrypted key cards and fobs to prevent long-rang skimmers from copying credentials without authorization. In turn, your property is more secure and less susceptible to intruders with falsified credentials.
Alternatives to RFID credentials
While the risk of RFID skimming is low, tenants might be preoccupied with the threat of skimming if your property uses RFID credentials. As an alternative, you might enable additional ways to open the door, like smartphone-based access.
A resident’s primary concern with an RFID credential might be the threat of a long-range EM RFID skimmer. However, as a property manager, RFID credentials like fobs or cards present a different set of problems.
An RFID fob might enable features like wireless or contactless entry with and higher levels of security. But there’s one way an RFID fob and an old-school brass key are the same: residents might still lose them.
So, to cut down on time spent on key management, the best way to use RFID access on your property is in tandem with other methods of access. You might consider a cloud-based access control system with a smartphone app. Moreover, a smartphone-based system enables residents to enter their building even if they’ve lost one physical credential — such as an RFID card or fob.
Further, by cutting down on the number of RFID devices used on your property, you can spend less time on programming and issuing new RFID fobs to tenants and more time focused on tenant satisfaction.
Get your free quote!
Fill in the form below, and we'll email you right back.
Want a free quote?
Fill in the form below, and we'll email you right back.
You’ll be redirected shortly...